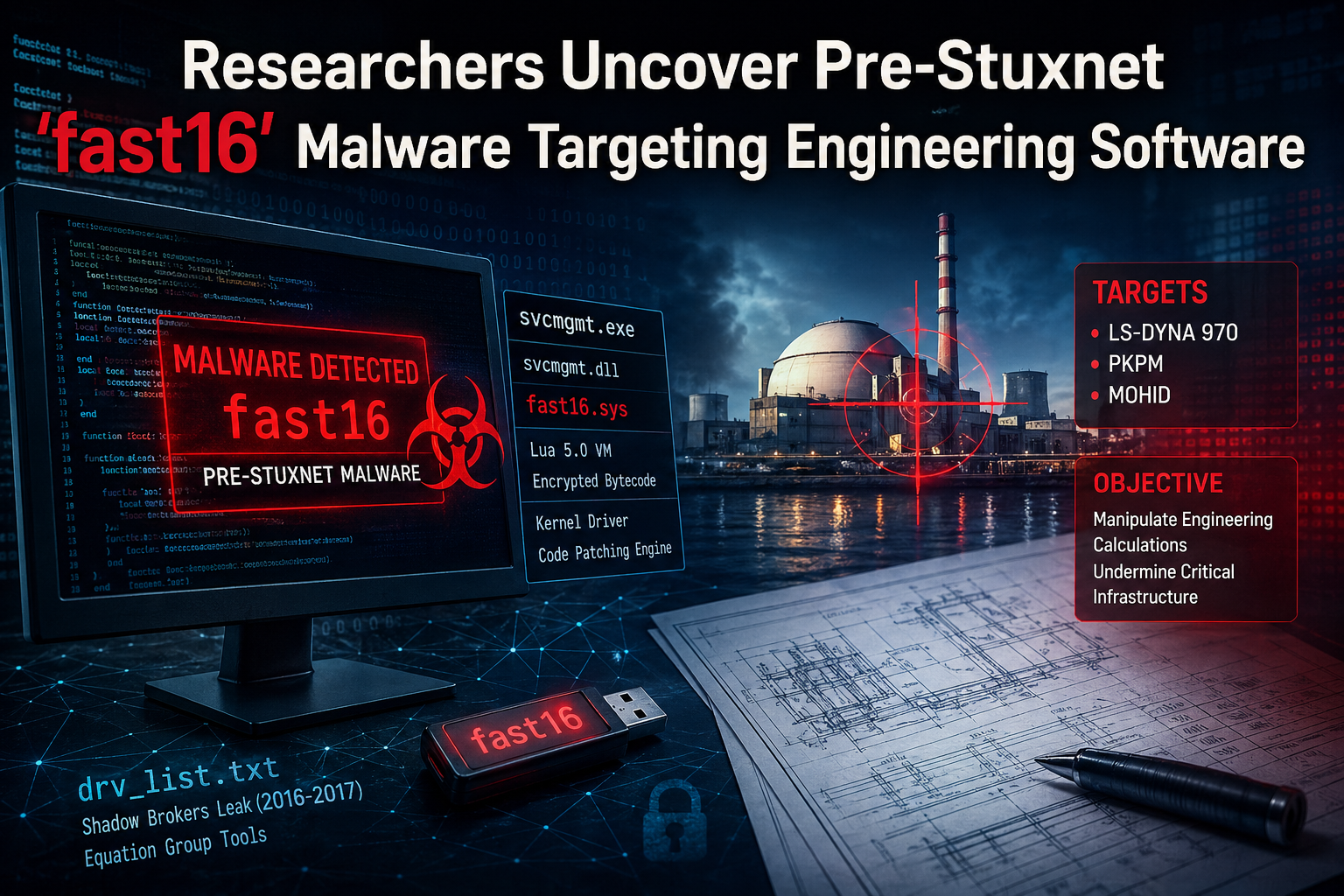
Cybersecurity experts have revealed details about an early cyber-sabotage malware framework known as fast16, which appears to have existed years before the infamous Stuxnet cyberweapon that targeted Iran’s nuclear infrastructure.
According to a detailed analysis highlighted by TAHN NEWS, the malware dates back to around 2005 and was engineered to manipulate high-precision engineering and scientific software by intentionally altering computational results. The research indicates that the attackers may have designed the malware to subtly influence calculations used in sensitive technical environments.
Security researchers Vitaly Kamluk and Juan Andrés Guerrero-Saade from SentinelOne explained that the malware framework combines payload execution with propagation techniques, enabling manipulated calculation results to spread throughout systems within the same network environment.
Early Cyber Sabotage Framework Discovered
The fast16 malware is believed to predate Stuxnet by approximately five years, suggesting that cyber-sabotage capabilities were already under development long before Stuxnet became known as the world’s first major digital weapon targeting industrial systems.
While Stuxnet has often been linked to joint cyber operations attributed to the United States and Israel, and later inspired related malware such as Duqu the newly analyzed fast16 framework indicates that similar cyber-attack concepts may have existed earlier than previously documented.
The discovery also predates Flame, another advanced malware platform uncovered in 2012. Flame utilized a Lua scripting environment, and the fast16 malware now appears to represent the earliest known Windows malware embedding a Lua virtual machine, making it a significant milestone in the evolution of sophisticated malware frameworks.
Investigation Reveals Hidden Malware Components
The discovery began when researchers analyzed a suspicious executable file named svcmgmt.exe. Initially, the file looked like a standard console-based Windows service wrapper. However, deeper examination uncovered several hidden components embedded inside the binary.
Investigators found that the executable included:
- A Lua 5.0 virtual machine
- An encrypted container storing compiled Lua bytecode
- Modules interacting with Windows NT system components, including file systems, services, registry entries, and network functions
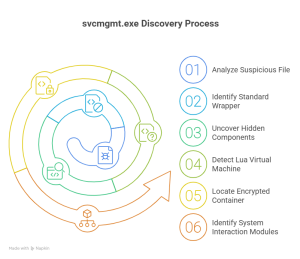
The malware’s main operational logic resides in encrypted Lua scripts executed by the embedded interpreter.
Additionally, researchers identified references to a kernel-level driver named fast16.sys, which appears to have been designed to intercept executable code as it loads from disk and modify it dynamically.
However, the driver does not function on Windows 7 or newer systems, indicating it was specifically built for earlier operating systems such as Windows 2000 and Windows XP.
Clues Linking fast16 to Leaked Cyber Arsenal Data
During the investigation, analysts discovered the string “fast16” within a leaked text file called drv_list.txt, which contains references to numerous drivers associated with advanced persistent threat (APT) operations.
This file reportedly surfaced during the Shadow Brokers leaks, a series of disclosures beginning in 2016–2017 that exposed hacking tools allegedly linked to the Equation Group, a sophisticated cyber-espionage unit widely believed to have connections to the U.S. National Security Agency (NSA).
The file was included in the massive archive of cyber tools published under the leak series known as “Lost in Translation.”
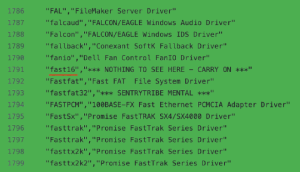
SentinelOne researchers explained that a forensic link between the leaked signatures and the svcmgmt.exe binary helped establish the timeline and potential origins of the fast16 framework.
Multi-Component Malware Architecture
The svcmgmt.exe file functions as a flexible “carrier module” capable of changing its behavior depending on command-line instructions.
This carrier component can:
- Run as a Windows service
- Execute embedded Lua scripts
- Deploy additional malware modules
The framework includes three major components:
- Lua bytecode payload – responsible for configuration management, coordination logic, and propagation
- svcmgmt.dll (ConnotifyDLL) – a helper module linked to network monitoring functions
- fast16.sys kernel driver – responsible for manipulating executable code
The malware also contains a self-propagation mechanism that scans local networks for vulnerable systems.
Worm-Like Propagation Across Networks
The malware includes a small propagation module known as an SCM wormlet, which attempts to spread across networked computers using weak or default authentication credentials.
The worm component scans for Windows systems and tries to copy itself onto machines running Windows 2000 or Windows XP.
Interestingly, the propagation process activates only under specific conditions. The malware first checks whether certain security products are installed by examining registry entries related to well-known antivirus vendors.
Security tools specifically checked by the malware include:
- Agnitum
- F-Secure
- Kaspersky
- McAfee
- Microsoft security products
- Symantec
- Sygate Technologies
- Trend Micro
If these defenses are detected, the propagation routine may remain inactive to reduce the risk of detection.
Network Monitoring and Communication Features
Another component of the malware, the ConnotifyDLL module, is triggered whenever the system establishes a new connection using Windows Remote Access Service (RAS).
When activated, the module records both the local and remote connection identifiers and writes them to a communication channel using a named pipe: \\.\pipe\p577
This mechanism allows attackers to monitor connection activity and potentially coordinate operations across compromised systems.
Precision Sabotage Through Code Manipulation
The most significant component of the framework is the fast16.sys kernel driver, which appears to be designed specifically for precision sabotage.
Instead of simply stealing information or disrupting systems, the driver intercepts executable programs compiled using the Intel C/C++ compiler.
It then modifies these programs using rule-based patching techniques, injecting malicious instructions into the program’s execution flow.
One notable function of the patching engine is the ability to introduce small calculation errors into scientific and engineering software.
Such manipulations could potentially affect programs used in fields such as:
- Civil engineering
- Physics simulations
- Industrial process modeling
Even minor inaccuracies introduced into scientific calculations could gradually degrade system performance, undermine research results, or cause structural failures over time.
Potential Targets Identified by Researchers
By analyzing the malware’s internal patching rules, researchers identified 101 different modification patterns targeting specific software applications.
Based on the rule set and the software ecosystem common during the mid-2000s, analysts believe the malware may have targeted three major engineering simulation tools:
- LS-DYNA 970 – a widely used multi-physics simulation platform
- PKPM – structural engineering design software
- MOHID – hydrodynamic modeling software used for environmental and oceanographic studies
LS-DYNA, now part of the Ansys simulation suite, is commonly used to model events such as crashes, impacts, and explosions.
In 2024, the Institute for Science and International Security (ISIS) reported that Iranian researchers had referenced modeling tools like LS-DYNA in academic papers related to nuclear engineering studies.
Connections to the Timeline of Cyber Warfare
The findings provide additional context for the timeline of cyber operations targeting Iran’s nuclear infrastructure.
Iran’s uranium enrichment facility at Natanz suffered significant damage in 2010 when the Stuxnet worm disrupted centrifuge operations.
Earlier research from Symantec also identified a preliminary Stuxnet version, known as Stuxnet 0.5—that targeted valve controls within the enrichment system as early as 2007, suggesting development activities dating back to 2005.
These discoveries suggest that advanced cyber-sabotage tools were already under development during the mid-2000s.
A New Perspective on Early Cyber Weapons
Security analysts say the discovery of fast16 reshapes our understanding of how cyber sabotage evolved.
The framework demonstrates that state-level cyber tools designed to manipulate real-world physical systems were already operational years before Stuxnet became publicly known.
Researchers conclude that fast16 represents a crucial link in the historical development of advanced cyber operations.
The malware illustrates how sophisticated actors design long-term covert tools capable of influencing physical infrastructure through software manipulation.
In many ways, fast16 appears to have quietly foreshadowed a new era of cyber strategy, where digital code could subtly shape events in the physical world.