Trust Wallet has confirmed that a second phase of the Shai-Hulud (also known as Sha1-Hulud) software supply chain attack, uncovered in November 2025, was likely behind the compromise of its Google Chrome browser extension, resulting in the theft of nearly $8.5 million worth of cryptocurrency assets.
In a post-incident analysis released on Tuesday, the company revealed that the attackers managed to expose internal developer secrets stored on GitHub, which ultimately gave them unauthorized access to the browser extension’s source code as well as Trust Wallet’s Chrome Web Store (CWS) API key.
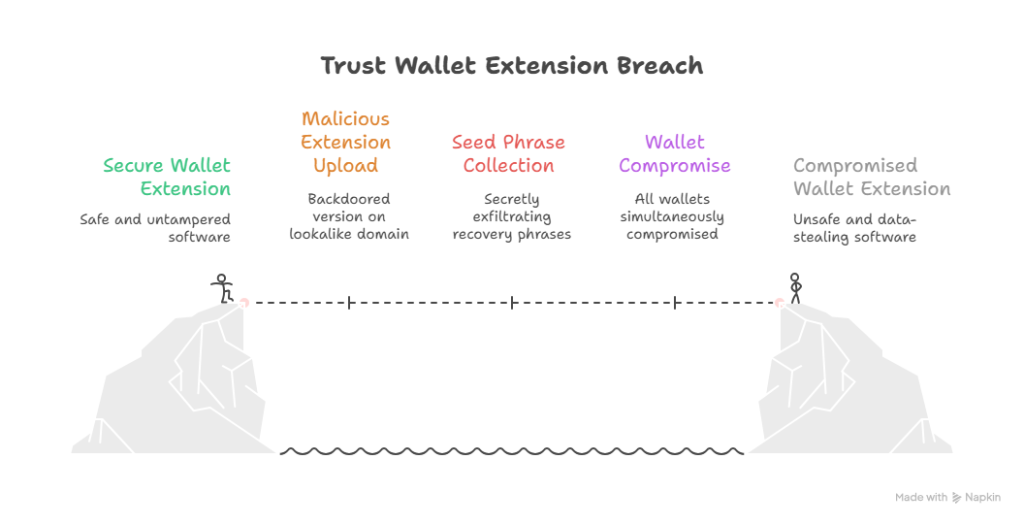
According to Trust Wallet, possession of the leaked API key allowed the attacker to gain full control over the Chrome Web Store publishing pipeline, enabling them to upload malicious builds without going through the company’s standard release process, which normally includes internal approvals and manual security reviews.
Trojanized Extension Delivered via Fake Metrics Domain
Following the breach, the threat actor reportedly registered a lookalike domain, metrics-trustwallet[.]com, and uploaded a backdoored version of the Trust Wallet Chrome extension. The malicious extension communicated with a subdomain, api.metrics-trustwallet[.]com, which was used to secretly collect users’ wallet recovery seed phrases.
Security firm Koi analyzed the injected code and discovered that the data-stealing logic was triggered every time the wallet was unlocked, not only during seed phrase imports. This meant that sensitive information was exfiltrated regardless of whether users authenticated using a password or biometric verification, and whether the extension had been actively used or simply opened once after being updated to version 2.68.
Researchers Oren Yomtov and Yuval Ronen explained that the malicious logic iterated through all wallets associated with a user account, not just the currently active one. As a result, users with multiple wallets configured had every wallet compromised simultaneously.
To avoid detection, the stolen seed phrases were hidden inside a field named errorMessage, embedded within what appeared to be routine unlock telemetry data. On the surface, the activity resembled a harmless analytics event tracking unlock success, making the malicious behavior easy to overlook during a cursory code inspection.
Infrastructure Tied to Bulletproof Hosting
Further investigation revealed that metrics-trustwallet[.]com resolved to the IP address 138.124.70.40, which is hosted by Stark Industries Solutions — a bulletproof hosting provider incorporated in the U.K. in February 2022, just weeks before Russia’s invasion of Ukraine.
The hosting provider has previously been associated with Russian state-linked cyber operations as well as a range of criminal infrastructure used by malware operators.
Koi researchers also noted an unusual response when directly querying the malicious server:
“He who controls the spice controls the universe,” a reference to the Dune franchise. Similar references were previously observed during the original Shai-Hulud npm supply chain incident, reinforcing the attribution.
Analysis of HTTP headers further showed that the attacker’s infrastructure had been prepared as early as December 8, more than two weeks before the malicious extension update was published on December 24, 2025. This timing strongly suggests the operation was carefully planned rather than opportunistic.
Malicious Update Impacted Over 2,500 Wallets
The disclosure follows Trust Wallet’s earlier warning urging nearly one million Chrome extension users to immediately upgrade to version 2.69, after the compromised version 2.68 was discovered on the Chrome Web Store.
The malicious update ultimately led to the draining of approximately $8.5 million in cryptocurrency from 2,520 wallet addresses, with the stolen funds consolidated into at least 17 attacker-controlled wallets. The first reports of wallet-draining activity surfaced just one day after the trojanized update was released.
Trust Wallet has since launched a reimbursement claim process for affected users. The company stated that all claims are being reviewed individually, noting that verification is necessary to distinguish legitimate victims from potential fraud attempts. As a result, processing timelines may vary.
Strengthened Security Measures and Industry-Wide Implications
In response to the incident, Trust Wallet said it has implemented additional safeguards and monitoring controls across its release and deployment pipelines to reduce the risk of similar compromises in the future.
The company emphasized that Sha1-Hulud was not a Trust Wallet–specific incident, but rather a widespread supply chain attack that impacted organizations across multiple industries, including cryptocurrency platforms.
The attack relied on compromised developer tooling and trusted dependencies, allowing threat actors to infiltrate environments indirectly rather than attacking companies head-on.
Meanwhile, security researchers have observed the emergence of Shai-Hulud 3.0, a newer iteration of the malware that features enhanced obfuscation techniques, improved error handling, and better Windows compatibility.
According to Upwind researchers Guy Gilad and Moshe Hassan, the latest version focuses on increasing stealth and operational longevity, while continuing its primary mission of stealing sensitive credentials and secrets from developer systems, rather than introducing entirely new exploitation methods.




