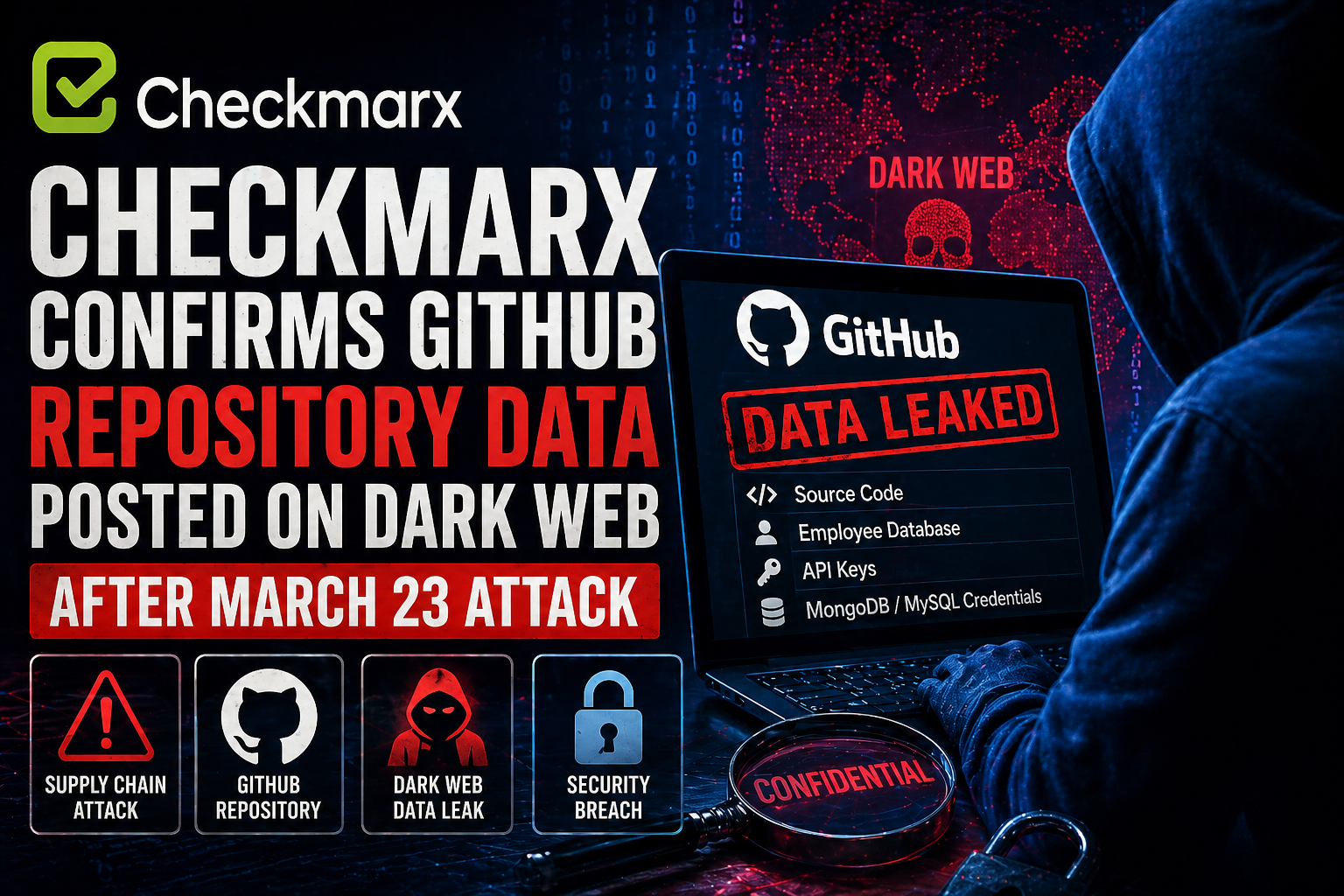
Checkmarx has confirmed that its ongoing investigation into a recent supply chain security incident has uncovered evidence that data associated with the company has been published on the dark web by a cybercriminal group.
“Based on the information currently available, we believe the exposed data originated from Checkmarx’s GitHub repository, and that unauthorized access to this repository was made possible through the supply chain attack that occurred on March 23, 2026,” the Israel-based cybersecurity Company stated.
The company clarified that this GitHub repository operates independently from its production systems and does not store customer-related data. Checkmarx also noted that its forensic investigation is still in progress as it continues to assess the full extent and nature of the leaked information.
As part of its incident response measures, access to the impacted GitHub repository has been restricted.
“If our investigation confirms that any customer data has been affected, we will promptly inform all impacted customers and relevant stakeholders,” the company added.
The update follows claims shared by Dark Web Informer on X, where the LAPSUS$ cybercrime group listed multiple victims on its leak platform, including Checkmarx. According to the listing, the compromised data may include source code, employee records, API keys, and database credentials such as MongoDB and MySQL.
The breach reportedly occurred after the Trivy supply chain attack late last month. During that incident, attackers manipulated two GitHub Actions workflows and two plugins distributed through the Open VSX marketplace, embedding a credential-stealing component capable of collecting various developer secrets.
Responsibility for the attack has been attributed to a threat actor identified as TeamPCP.
More recently, the same financially motivated group is believed to have further expanded its attack by compromising Checkmarx’s KICS Docker image, in addition to the previously affected VS Code extensions and GitHub Actions workflow. This extended compromise triggered a chain reaction that briefly impacted the Bitwarden CLI npm package.