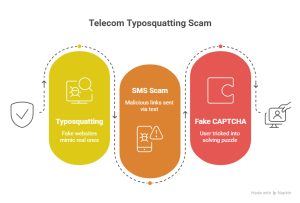
Cybersecurity researchers have revealed detailed insights into a large-scale telecommunications fraud campaign that leverages fake CAPTCHA verification techniques to trick users into sending international SMS messages. These messages result in unexpected charges on mobile bills, generating unlawful revenue for threat actors who control or lease premium-rate phone numbers.
According to a recent report by Infoblox, the campaign has likely been active since June 2020. It uses advanced social engineering tactics, including browser back button manipulation, to increase user engagement and success rates. Investigations have identified at least 35 phone numbers across 17 countries linked to this international revenue share fraud (IRSF) activity.
“The fake CAPTCHA involves multiple stages, and each interaction is preconfigured with numerous phone numbers. As a result, victims may unknowingly send messages to dozens of international destinations,” researchers David Brunsdon and Darby Wise explained.
They further noted that delayed billing cycles make detection more difficult, as charges may only appear weeks later, long after the interaction has been forgotten.
A key aspect of this threat is the combination of IRSF techniques with malicious traffic distribution systems (TDS). Traditionally used to redirect users toward malware or phishing pages, TDS infrastructure is now being adapted to scale SMS-based fraud campaigns globally.
IRSF schemes typically involve acquiring access to international premium-rate numbers and artificially increasing traffic (calls or messages) to these numbers. Telecom operators are then required to pay termination fees to destination networks, a portion of which is shared with fraudsters.
In this campaign, attackers strategically register phone numbers in regions known for higher termination fees or less strict regulatory oversight, including Azerbaijan, Kazakhstan, and select European countries. This enables higher profit margins from each fraudulent interaction.
The attack sequence begins when a user is redirected, often through a commercial TDS, to a fraudulent webpage displaying a CAPTCHA prompt. The page instructs users to send an SMS to verify they are human. This initiates a multi-step verification process where SMS applications on Android or iOS devices are triggered automatically with pre-filled details.
In some cases, victims may send up to 60 SMS messages to multiple international numbers through a series of steps, potentially costing around $30. While this may appear minimal individually, the scale of operations significantly amplifies profits for threat actors.
The campaign also utilizes browser cookies to monitor user progress within the verification flow. Specific cookie values determine whether a user continues through the scam or is redirected to alternative campaigns.
Another notable technique is back button hijacking. Through JavaScript manipulation, attackers alter browser history to prevent users from exiting the fraudulent page. Attempts to navigate away simply redirect users back into the scam flow, effectively trapping them unless the browser is fully closed.
“This campaign impacts both individuals and telecom providers,” Infoblox reported. “Users face unexpected charges, while telecom operators may incur financial losses through disputes and chargebacks.”
How Threat Actors Abuse Keitaro TDS
This disclosure aligns with further research conducted by Infoblox in collaboration with Confiant, highlighting how Keitaro TDS (also known as Keitaro Tracker) is being exploited by cybercriminal groups.
Keitaro is originally designed as a self-hosted advertising performance tracking platform that routes traffic based on predefined conditions. However, threat actors have repurposed it into a multi-functional tool capable of acting as a traffic distribution system, cloaking mechanism, and campaign tracker.
In some instances, attackers obtain unauthorized access to Keitaro through compromised or illegally distributed licenses. These setups are then used to distribute malicious content, including malware, cryptocurrency scams, and fraudulent investment platforms.
A significant portion of these campaigns is promoted through paid advertising channels such as Facebook Ads. Victims are redirected to fake AI-powered investment platforms promising high returns. These scams often include fabricated endorsements, fake news articles, and synthetic media to increase credibility.
One identified threat group, referred to as FaiKast, has been linked to the use of deepfake technology in promotional materials, further enhancing the illusion of legitimacy.
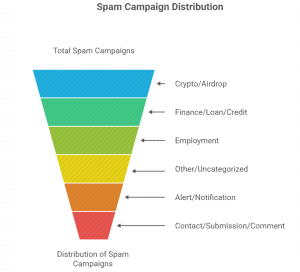
Over a four-month period from October 2025 to January 2026, researchers identified more than 120 distinct campaigns utilizing Keitaro TDS. During this timeframe, over 226,000 DNS queries were recorded across approximately 13,500 domains associated with these activities.
Following responsible disclosure, Keitaro has taken action by disabling multiple accounts connected to fraudulent operations.
Researchers also found that nearly 96% of Keitaro-related spam campaigns were focused on cryptocurrency-related fraud. These included wallet-draining schemes disguised as airdrops or giveaways, commonly targeting platforms and tokens such as AURA, Solana (SOL), Phantom Wallet, and Jupiter exchange services.
“By combining traditional investment fraud strategies with modern AI-driven deception techniques, threat actors have created highly scalable and convincing cyber campaigns,” researchers concluded.