Cybersecurity researchers have flagged a series of attacks carried out by a pro-Ukrainian hacktivist group known as PhantomCore, targeting servers running TrueConf video conferencing software in Russia since September 2025.
According to a report published by Positive Technologies, the threat actors are leveraging an exploit chain consisting of three vulnerabilities to execute remote commands on vulnerable servers.
“Despite the fact that there are no exploits for this chain of vulnerability in public access, attackers from PhantomCore managed to conduct their research and reproduce vulnerabilities, which led to a large number of cases of its operation in Russian organizations,” researchers Daniil Grigoryan and Georgy Khandozhko said.
PhantomCore, also known as Fairy Trickster, Head Mare, Rainbow Hyena, and UNG0901, is a politically- and financially-motivated hacking group that has been active since 2022 following the Russo-Ukrainian war. The group is known for stealing sensitive data and disrupting targeted networks, sometimes deploying ransomware based on leaked source code from Babuk and LockBit.
“The group runs large-scale operations while maintaining strong stealth, remaining undetected within victim networks for extended periods, enabled by continuous updates and evolution of in-house offensive tools,” the company noted in September 2025.
The TrueConf Server vulnerabilities exploited in these attacks include:
- BDU:2025-10114 (CVSS score: 7.5) – An insufficient access control vulnerability allowing unauthorized requests to administrative endpoints (/admin/*).
- BDU:2025-10115 (CVSS score: 7.5) – A vulnerability enabling attackers to read arbitrary system files.
- BDU:2025-10116 (CVSS score: 9.8) – A command injection vulnerability allowing execution of arbitrary operating system commands.
Successful exploitation of these vulnerabilities allows attackers to bypass authentication and gain unauthorized access to organizational networks. Although patches were released by TrueConf on August 27, 2025, the first attacks were detected in mid-September 2025.
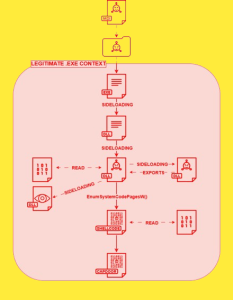
In observed incidents, compromised TrueConf servers were used as entry points to move laterally across internal networks. Attackers deployed malicious payloads to support reconnaissance, evade defenses, harvest credentials, and establish communication channels via tunneling tools.
At least one confirmed attack involved deploying a PHP-based web shell capable of uploading files and executing remote commands. Additionally, a proxy-based PHP script was used to mask malicious traffic as legitimate server requests.
Other tools observed in these attacks include:
- PhantomPxPigeon, A malicious TrueConf client enabling reverse shell access and remote command execution.
- PhantomSscp (DLL), MacTunnelRat (PowerShell), PhantomProxyLite (PowerShell) – Used for establishing persistence via reverse SSH tunnels.
- ADRecon – Used for reconnaissance.
- Veeam-Get-Creds, a Modified PowerShell script for extracting credentials from Veeam Backup & Replication systems.
- DumpIt and MemProcFS – Used for credential harvesting.
- Windows Remote Management (WinRM) and Remote Desktop Protocol (RDP) – Used for lateral movement.
- Velociraptor, Used for remote access.
- microsocks, rsocx, and tsocks Used to control compromised systems via SOCKS proxy infrastructure.
In some cases, attackers deployed a malicious DLL to create a rogue administrative user named “TrueConf2” on compromised servers.
PhantomCore has also used phishing campaigns as an initial access vector, distributing ZIP and RAR archives containing backdoors capable of executing remote commands and delivering additional payloads.
“The PhantomCore group is one of the most active threat actors in the Russian cyber landscape,” researchers noted. “It utilizes both publicly available and proprietary tools to target government and private organizations across multiple industries.”
Recent activity also highlights attacks targeting industrial and aviation sectors by another group known as CapFIX. This group uses phishing campaigns to deploy a backdoor called CapDoor, capable of executing PowerShell commands, installing software, and capturing screenshots.
Further analysis reveals CapFIX leveraging ClickFix techniques to distribute malware such as AsyncRAT and SectopRAT.
“While the group previously relied on financially themed phishing emails, they are increasingly disguising messages as official government communications,” researchers added.
Additional threat groups targeting Russian entities include:
- Geo Likho – Targeting aviation and shipping sectors using phishing-based malware attacks.
- Mythic Likho – Deploying advanced loaders and backdoors linked to the Havoc framework.
- Paper Werewolf (GOFFEE) – Using Telegram-based distribution of trojans and phishing pages.
- Versatile Werewolf (HeartlessSoul) – Delivering malware through fake software tools and malicious installers.
- Eagle Werewolf – Distributing Rust-based malware through compromised Telegram channels.
“Despite similar objectives, these threat groups operate independently without direct coordination,” cybersecurity experts noted.
“In addition to malware distribution, some groups hijack Telegram accounts to facilitate future attacks, while others leverage AI technologies to accelerate malware development.”