A newly uncovered investigation has revealed that a Vietnam-linked cyber operation leveraged Google AppSheet as a “phishing relay” to distribute large volumes of phishing emails aimed at compromising Facebook accounts.
This activity has been labeled “AccountDumpling” by Guardio. The attackers are not only stealing accounts but also reselling them through illicit online storefronts operated by the same group. Estimates suggest that nearly 30,000 Facebook accounts have been compromised during this campaign.
According to security researcher Shaked Chen, this is far from a basic phishing kit. Instead, it represents a live, continuously evolving operation featuring real-time operator panels, advanced evasion techniques, and ongoing updates. The entire system functions as a criminal-commercial loop that monetizes the same accounts it helps compromise.
These findings highlight a broader trend in which Vietnamese threat actors are increasingly adopting diverse tactics to gain unauthorized access to Facebook accounts, which are later sold across underground marketplaces for financial gain.
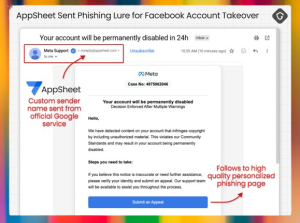
The attack chain begins with a phishing email specifically targeting Facebook Business account owners. The message impersonates Meta Support and warns recipients that their account may be permanently deleted unless they submit an appeal immediately.
These emails are sent from a Google AppSheet address (“noreply@appsheet.com”), allowing them to bypass standard spam filters and appear more legitimate to recipients.
The false sense of urgency directs users to a fraudulent webpage designed to capture login credentials. Similar campaigns using comparable techniques were also reported in May 2025.
In recent weeks, attackers have deployed multiple lures designed to trigger what can be described as “Meta-related panic.” These include account suspension warnings, copyright violation notices, verification prompts, executive recruitment messages, and suspicious login alerts.
Guardio categorized the campaign into four primary clusters:
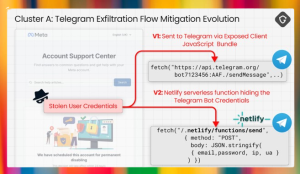
Netlify-hosted fake Facebook help pages that not only facilitate account takeover but also collect sensitive information such as date of birth, phone numbers, and government-issued identification. This data is then forwarded to attacker-controlled Telegram channels.
Blue badge verification scams that direct victims to Vercel-hosted “Security Check” or “Meta Privacy Center” pages. These pages employ fake CAPTCHA challenges before redirecting users to phishing pages where credentials and two-factor authentication (2FA) codes are harvested.
Google Drive-hosted PDF documents disguised as account verification instructions. These PDFs, generated using free Canva accounts, trick users into providing passwords, 2FA codes, ID images, and browser screenshots.
Fake job offers in which attackers impersonate well-known companies such as WhatsApp, Meta, Adobe, Pinterest, Apple, and Coca-Cola to build trust and guide victims toward malicious platforms.
Collectively, Telegram channels associated with these campaigns contain data from approximately 30,000 victims. A significant portion of affected users are located in the United States, Italy, Canada, the Philippines, India, Spain, Australia, the United Kingdom, Brazil, and Mexico, many of whom have been locked out of their accounts.
Attribution efforts uncovered a key clue within the metadata of the Canva-generated PDFs, which listed the name “PHẠM TÀI TÂN” as the author. Further open-source intelligence led to the discovery of a website offering digital marketing services, potentially linked to the operation.
A social media post from February 2023 associated with the same entity claimed specialization in digital marketing services and strategic consulting.
Taken together, the evidence suggests a large-scale Vietnamese operation that extends beyond simple AppSheet abuse and reflects a broader underground economy.
Within this ecosystem, Facebook account access, business identity, advertising reputation, and even account recovery services have become tradable commodities. This campaign serves as yet another example of how trusted platforms are being repurposed for delivery, hosting, and monetization in cybercriminal activities.